CDEXOS Overview: In the fast-paced and constantly evolving world of technology, organizations should have a clear and effective cybersecurity strategy for managing threats – Enter the OODA Loop! The OODA loop (Observe, Orient, Decide, and Act) was developed by military strategist and United States Air Force Colonel John Boyd. In this article, we will discuss how the OODA Loop can be used to anticipate and respond to attacks in a proactive and effective manner… Enjoy!
The OODA Loop as Cybersecurity Strategy
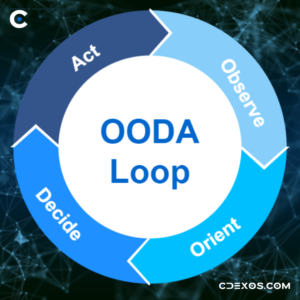
The OODA loop stands for Observe, Orient, Decide, and Act, and it describes the four steps that an individual or organization goes through when making a decision in an uncertain and rapidly changing environment. In the context of cybersecurity, the OODA loop can be used to guide the process of responding to a cyber threat.
- The first step in the OODA loop is Observe. This involves actively collecting information about the threat and the environment in which it is occurring. This could include monitoring network traffic, analyzing log files, and gathering intelligence about the threat itself. It’s important to have a robust system in place for gathering this information, as it will be critical to understanding the nature of the threat and determining an appropriate response.
- The second step is Orient. In this step, the information gathered during the Observe step is used to create a mental model of the situation. This helps the decision-maker understand the context in which the threat is occurring, and what options are available for responding to it. The Orient step is particularly important in cybersecurity, as it allows the organization to identify the specific vulnerabilities that the threat is exploiting and determine the best course of action to mitigate those vulnerabilities.
- The third step is Decide. Based on the information gathered and the mental model developed in the Orient step, the decision-maker chooses a course of action. This could involve implementing a specific security measure, such as blocking a particular IP address or shutting down a compromised system. It’s important to have a clear and defined process in place for making decisions in the face of a cyber threat, as this can help to ensure that the organization responds in a timely and effective manner.
- The fourth/final step is Act. This involves taking the action decided upon in the Decide step. This could involve executing a specific security measure, communicating the threat to relevant parties, or initiating an incident response plan. It’s important to have a clear plan in place for executing the chosen course of action, as this can help to ensure that the response is carried out smoothly and effectively.
OODA Loop for Cybersecurity Strategy Refinement
It’s worth noting that the OODA loop is not a one-time process, but rather a continuous-improvement cycle. As new cybersecurity threat information becomes available, the organization will need to go through the loop again, updating its mental model and adjusting its response as necessary. This can be particularly challenging in the context of cybersecurity, as new threats are constantly emerging and the landscape is constantly changing.
CDEXOS Summary
By following the four steps of Observe, Orient, Decide, and Act, organizations can make informed and strategic decisions in the face of rapidly changing and uncertain circumstances. By implementing a robust and well-defined process for following the OODA loop, organizations can better protect themselves and their assets against the ever-present threat of cyber attacks. Let CDEXOS provide you with a complementary Cybersecurity Assessment by completing our request form today!
Sam Palazzolo, Founder/CEO
