CDEXOS Overview: In an increasingly interconnected and digital world, the threat landscape is evolving at an alarming pace, presenting formidable challenges for businesses and individuals alike. Cybersecurity has become a critical concern for organizations as they grapple with the ever-present risk of cyber attacks. To combat these threats, a proactive and multidimensional approach is essential. This article explores the symbiotic relationship between incident response, threat intelligence, and cyber training, and how their fusion can empower organizations to prevail in the face of cyber threats…Enjoy!
Your Cybersecurity Solution Starts Here!
You need to evolve your Cybersecurity protection, but where do you start? CDEXOS helps organizations identify, protect and respond to cyber threats. Our mission prioritizes business decisions so you make informed decisions on data protection, cloud migration, and cybersecurity.
The Imperative for a Holistic Approach
In today’s hyper-connected world, the digital landscape is no longer confined to traditional boundaries. Cybercriminals are increasingly sophisticated, leveraging advanced techniques to breach security defenses. As a result, organizations must move beyond traditional reactive measures and adopt a holistic approach to cybersecurity.
Incident Response: Swift Action to Minimize Damage
Incident response is the first line of defense in the battle against cyber threats. It involves a well-defined plan and a skilled team ready to respond swiftly and decisively when an attack occurs. The goal is to minimize the impact of an incident, contain the threat, and restore normal operations as quickly as possible.
A robust incident response framework incorporates three key elements: detection, containment, and recovery. Detection involves monitoring systems and networks for signs of a breach, using advanced technologies like intrusion detection systems and security information and event management (SIEM) tools. Containment focuses on isolating compromised systems, preventing the attacker from spreading further within the network. Recovery encompasses the restoration of affected systems, data, and services to their pre-incident state.
Threat Intelligence: Knowledge as Power
Threat intelligence plays a crucial role in understanding the threat landscape and anticipating potential attacks. By gathering information about emerging threats, vulnerabilities, and attacker techniques, organizations can proactively fortify their defenses and stay one step ahead of cybercriminals.
Threat intelligence is not limited to the data collected within an organization; it extends to external sources such as cybersecurity vendors, information sharing communities, and government agencies. By leveraging this collective intelligence, organizations can identify patterns, recognize indicators of compromise, and develop proactive strategies to mitigate risks.
Cyber Training: Empowering the Human Firewall
While technology plays a significant role in cybersecurity, the human element remains a critical factor. Cybercriminals often exploit human vulnerabilities through techniques like social engineering and phishing attacks. Cyber training is vital to empower employees and enhance their cybersecurity awareness, turning them into the organization’s first line of defense.
Comprehensive cyber training programs encompass a range of topics, including recognizing phishing attempts, creating strong passwords, practicing safe browsing habits, and adhering to data protection policies. Regular training sessions, simulated phishing campaigns, and knowledge assessments help reinforce best practices and ensure that employees are equipped to identify and respond to potential threats.
The Dynamic Fusion: Synergy in Action
While incident response, threat intelligence, and cyber training are effective in isolation, their true power lies in their dynamic fusion. By integrating these three elements, organizations can create a robust cybersecurity ecosystem that adapts and evolves to counter emerging threats.
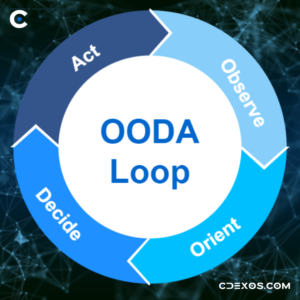
The synergy between incident response, threat intelligence, and cyber training can be illustrated in a cyclical model. Incident response teams analyze and extract intelligence from cyber incidents, contributing to threat intelligence repositories. This knowledge is then shared with the training department, which tailors training programs to address specific threats and vulnerabilities identified. In turn, cyber training equips employees to be more vigilant, reducing the likelihood and impact of future incidents.
The Path to Prevailing in the Cyber Battleground
In the relentless cyber battleground, organizations must embrace a proactive and adaptive approach. To prevail against cyber threats, they need to:
Foster Collaboration
Encourage collaboration and communication between incident response teams, threat intelligence analysts, and the training department. Regular meetings, shared insights, and joint exercises enhance the flow of information and enable a more holistic understanding of the evolving threat landscape.
Embrace Automation and AI
Leverage automation and artificial intelligence (AI) technologies to augment incident response capabilities and threat intelligence analysis. Automated incident detection and response systems can quickly identify and contain threats, while AI-powered algorithms can process vast amounts of data to identify patterns and anomalies, enhancing threat intelligence efforts.
Engage in Continuous Monitoring
Implement continuous monitoring of systems and networks to detect potential vulnerabilities and indicators of compromise. Real-time visibility into network traffic, log data, and user behavior enables organizations to identify and respond to threats before they escalate.
Prioritize Employee Education
Cyber training should be an ongoing and integral part of an organization’s cybersecurity strategy. Regularly update training programs to address emerging threats and equip employees with the knowledge and skills to recognize and respond to evolving attack techniques effectively.
Engage External Partners:
Collaborate with external cybersecurity partners, such as managed security service providers (MSSPs), threat intelligence vendors, and incident response teams. These partnerships can provide access to specialized expertise, advanced technologies, and up-to-date threat intelligence, augmenting an organization’s cybersecurity capabilities.
Conduct Red Team Exercises
Regularly conduct red team exercises to simulate real-world cyber attacks and test the effectiveness of incident response plans and training programs. These exercises help identify vulnerabilities, validate response strategies, and enhance preparedness for actual incidents.
Stay Abreast of Regulatory Requirements
Keep up to date with regulatory requirements and industry standards related to cybersecurity. Compliance with data protection regulations not only helps protect sensitive information but also fosters trust among customers and stakeholders.
CDEXOS Summary
In the face of an ever-evolving threat landscape, the fusion of incident response, threat intelligence, and cyber training provides a powerful defense against cyber threats. Organizations that embrace a proactive and holistic approach to cybersecurity can effectively mitigate risks, minimize the impact of incidents, and maintain the trust of their customers and stakeholders. The synergy between incident response, threat intelligence, and cyber training empowers organizations to stay one step ahead of cybercriminals and protect their valuable assets in the digital age.
Let CDEXOS provide you with a complementary Cybersecurity Assessment by completing our request form today!
Sam Palazzolo, Founder/CEO