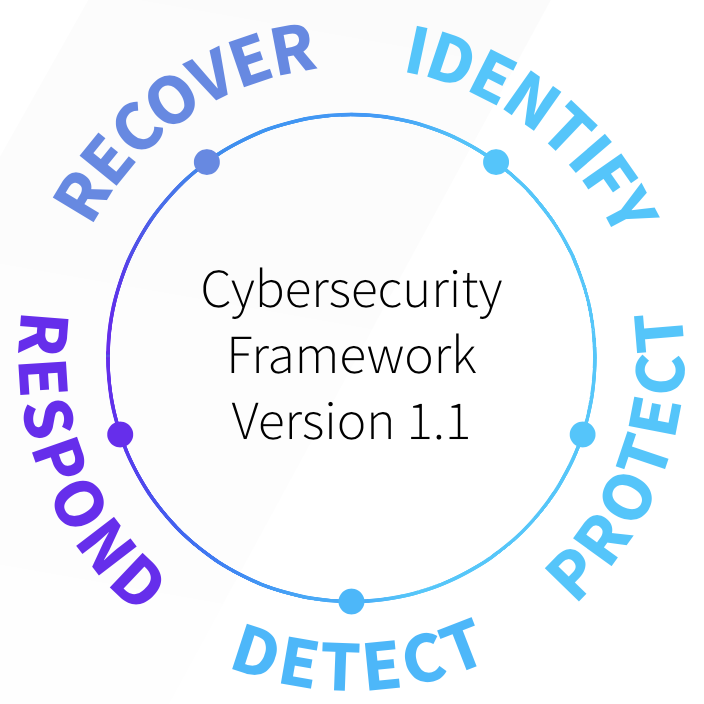
Security teams cannot protect assets they don’t know about. The main goal of the Identify function is to help organizations understand their environment and then prioritize their efforts in later stages. Mandated compliance standards and audits often create the baseline for these efforts. In the long run, the identification phase enables teams to be able to protect their stakeholders and their shareholders.
Activities in this function include:
- Asset Management – Continuous, long-term project, led by IT
- Business Environment – Short annual project, led by Security
- Governance, Risk Assessment – Short annual project, led by Security
- Risk Management Strategy – Short quarterly project, led by Security
- Supply Chain Risk Assessment – Medium project with smaller ongoing projects, led by Security
In essence, companies need to know what devices and services are a part of the internal IT landscape to secure them. It might sound self-apparent, but maintaining an accurate inventory is often an uphill battle given the constant, dynamic changes that allow companies to stay relevant in a competitive marketplace! Simply keeping a personnel roster while rapidly hiring and releasing employees is a challenge without the complexity that comes from mergers/ acquisitions, equipment replacement, deploying new services in an agile environment.
To build out their Identify function, companies often turn to specialists in the field to evaluate their security posture. Those specialists, cyber security consultants, often conduct a myriad of both technical assessments and professional services discovery to truly understand the current risk posture. Cyber security consultants often assess the company’s overall security program beginning with how the company earns its revenue and the security policies that enable them
to go to market. Next, they conduct a technical assessment that can include employee interviews, technical scans, penetration tests, risk assessments, and gap analyses (often with the NIST CSF). While an organization may have goals for their security maturity, they may not have the talent or time to achieve those goals by themselves. One outcome of those assessments is often a prioritized, multi-year roadmap that helps the company “move the needle” in security and helps turn the overall vision into manageable projects.