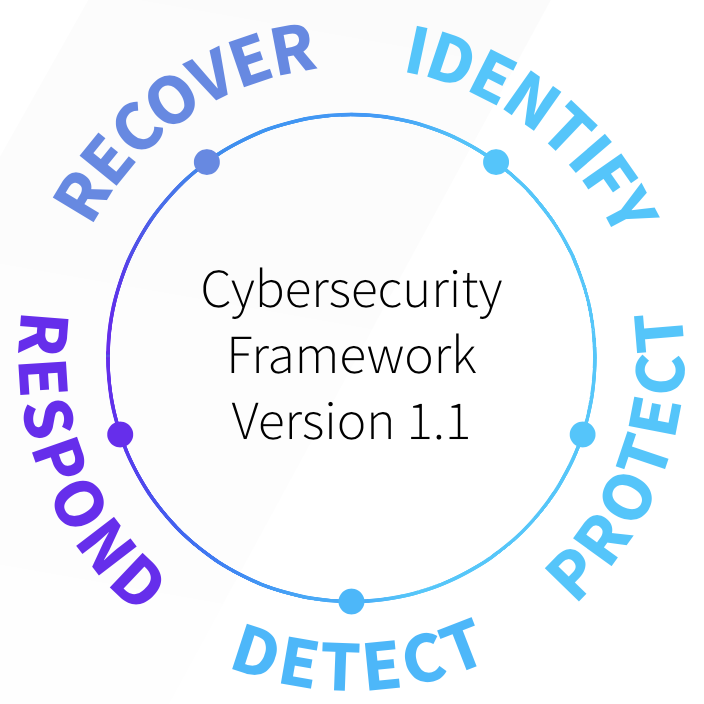
The next function is Detect, which encourages implementing practices that quickly recognize abuse by monitoring for system anomalies. Managed detection and response (MDR) and dark web monitoring are two examples of solutions designed for the Detect function. Activities in the Detect function include:
- Anomalies and events – Long term continuous project, led by Security
- Security Continuous Monitoring – Long term continuous project, led by Security
- Detection Processes – Long term continuous project, led by Security
The Detect function is traditionally led by Security and is where most organizations fail to hire, train, and retain talent internally that can monitor systems 24/7. One of the largest issues in the Detect phases is known as “alert fatigue” where Detection tools generate so many alerts that practitioners are drowned in a sea of false alarms. Often their response is to “tune” their sensors to the point that the sensors simply do not alert for anything. This happens often enough that IT business leaders question the efficacy of their own program and begin to explore outsourcing the Detect function.